WARNING: GateIn integration with Salesforce and Google Apps is now documented in GateIn reference guide https://docs.jboss.org/author/display/GTNPORTAL36/SAML2 where are latest informations. This wiki page is no longer maintained and may have outdated info.
From version 3.3, GateIn supports SAML SSO integration. This integration is available in GateIn SSO component and more details about it can be found in Reference guide . GateIn SSO is leveraging library Picketlink Federation for the implementation of SAML specification, which currently supports integration with 3rd party SAML vendors like Salesforce or Google Apps .
Latest version 1.2.0-Beta01 of GateIn SSO component, which can be downloaded here contains the support for Salesforce and Google Apps integration. So if you don't have time to wait for GateIn 3.4 you can try latest SSO component and latest GateIn reference guide from GateIn master and try the integration. Supported scenarios are:
- GateIn portal as SAML Identity Provider, Salesforce as SAML Service Provider
- GateIn portal as SAML Identity Provider, Google Apps as SAML Service Provider
- GateIn portal as SAML Service Provider, Salesforce as SAML Identity Provider
In next sections, you can see detailed description of all scenarios with needed configuration changes.
GateIn as SAML IDP, Salesforce as SAML SP
- Base configuration of GateIn as IDP - first you need to configure GateIn as SAML IDP as described in Reference guide in very last tutorial (GateIn as SAML IDP).
- Common steps for Salesforce integration are described in Picketlink documentation and they are quite similar for GateIn like for another web application. Here we describe only steps different for GateIn, which can be divided into configuration on Salesforce side and configuration on GateIn side:
Salesforce configuration
- In Salesforce setup in SSO configuration, you need to configure Issuer, Identity Provider Login URL and Identity Provider Logout URL to value http://www.node1.com:8080/portal/dologin (Assuming that you are using virtual host www.node1.com as described in SAML scenario in GateIn Reference guide)
- Certificate - you need to import correct certificate into Salesforce. It needs to be certificate, which is used for signing of SAML messages from GateIn. You can export certificate from directory JBOSS_HOME/server/portal-idp/deploy/gatein.ear/02portal.war/WEB-INF/classes with command:
keytool -export -file portal-idp.crt -keystore idp-keystore.jks -alias idp-key
This certificate then needs to be imported into Salesforce. Again, we assumed that you followed steps in Reference guide example. Otherwise change command according to name of your keystore and signing key aliases.
- Create some users in your Salesforce domain, which are available in GateIn as well. You can use inverse approach as well and create users in GateIn, which are present in Salesforce. Important is mapping - username in GateIn is mapped to Federation ID in Salesforce. So for example GateIn user mary is mapped to Salesforce user in your domain, which has Federation ID mary .
GateIn configuration
- Make sure you import Salesforce client certificate into your GateIn keystore. Command for doing it can looks like:
keytool -import -keystore idp-keystore.jks -file /tmp/proxy-salesforce-com.123 -alias salesforce-cert
- Configure ValidatingAlias, Trusted domains and Metadata in same way like for base Picketlink tutorial
Test the integration - After configure both IDP and SP, you can test that after accessing URL of your Salesforce domain like https://yourdomain.my.salesforce.com , SAML Request will be sent to GateIn and you will be redirected to your virtual host to GateIn login screen on http://www.node1.com:8080/portal/dologin . You can login with some GateIn user (like mary) and you should be redirected back to Salesforce and automatically logged here as user mary thanks to SAML SSO.
GateIn as SAML IDP, Goggle Apps as SAML SP
Again, we assume that you followed GateIn reference guide and the last section for GateIn as Identity Provider.
The common steps for Google Apps integration with classic web application are again described in Picketlink guide, so we will pay attention on steps specific for GateIn.
Google configuration
- Create some users in Google Apps, which are available in GateIn as well (or vice-versa). Username in GateIn is mapped to nick in Google Apps. For example GateIn user mary is standardly mapped to Google Apps user mary@yourgoogledomain.com , which normally has nick mary .
- In SSO configuration of Google Apps domain, you need to change all Sign-In and Sign-Out URL to value http://www.node1.com:8080/portal/dologin instead of default http://localhost:8080/idp-sig (Assuming that you are using virtual host www.node1.com as described in SAML tutorial in GateIn Reference guide)
GateIn configuration
- General configuration - you need to configure metadata and Trust domains in similar way like in Picketlink tutorial . No GateIn specific steps here.
Test the integration - when you want to access your Google Apps domain, SAML Request will be sent to GateIn on your host like http://www.node1.com:8080/portal/dologin and after login with GateIn username, you will be again redirected to Google Apps with SAML Response and you should be automatically logged to Google Apps thanks to SAML SSO.
GateIn as SAML SP, Salesforce as SAML IDP
We assume that you followed GateIn Reference guide and configured GateIn as SP in JBoss configuration node1 as described in tutorial with GateIn as SAML SP. Also the common steps for Salesforce integration with classic web application are again described in Picketlink guide, so we will pay attention especially on steps specific to GateIn.
Salesforce configuration
- Disable SSO in Salesforce - Like in generic Picketlink guide, you need to disable SSO in Salesforce, because now we don't want Salesforce to act as SP but as IDP.
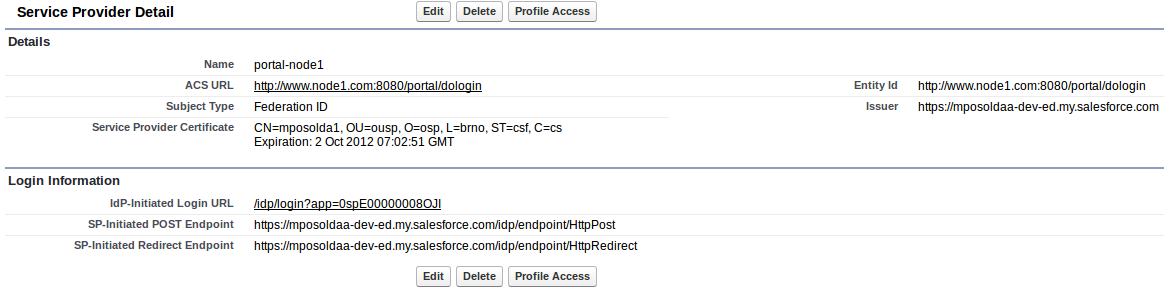
- Create GateIn Service Provider - It is also necessary to add GateIn Service Provider in configuration of Identity Provider in Salesforce. In Picketlink guide is described how to do it. Configuration for GateIn portal SP can look similarly like this (Assuming that GateIn SP will be executed on virtual host www.node1.com ):
GateIn configuration
- Certificate - Similarly like in base tutorial, we need to import certificate created by Salesforce into GateIn keystore.
- URL configuration - In JBOSS_HOME/server/node1/deploy/gatein.ear/02portal.war/WEB-INF/picketlink.xml you need to change URLs to values corresponding to Salesforce (or you can use System properties if don't want to edit the file):
<IdentityURL>https://yourdomain.my.salesforce.com/idp/endpoint/HttpPost</IdentityURL> <ServiceURL>http://www.node1.com:8080/portal/dologin</ServiceURL>
- ValidatingAlias can looks like this (assuming that you imported salesforce certificate into your keystore under alias salesforce-idp ):
<ValidatingAlias Key="yourdomain.my.salesforce.com" Value="salesforce-idp" />
- For roles-mapping, you don't need to configure nothing on GateIn because GateIn SP is configured by default to obtain roles from Picketlink IDM database and not from IDP SAML Response (but you are free to change this behaviour). So no changes needed
in comparison to normal JAAS login modules configuration for salesforce. Your JAAS configuration in JBOSS_HOME/server/node1/deploy/gatein.ear/META-INF/gatein-jboss-beans.xml can look like this:
<application-policy xmlns="urn:jboss:security-beans:1.0" name="gatein-domain"> <authentication> <login-module code="org.gatein.sso.agent.login.SAML2IntegrationLoginModule" flag="required"> <module-option name="portalContainerName">portal</module-option> <module-option name="realmName">gatein-domain</module-option> <module-option name="useSAMLRoles">false</module-option> <module-option name="password-stacking">useFirstPass</module-option> </login-module> <login-module code="org.exoplatform.services.security.j2ee.JbossLoginModule" flag="required"> <module-option name="portalContainerName">portal</module-option> <module-option name="realmName">gatein-domain</module-option> </login-module> </authentication> </application-policy>
- Test the integration - after startup of GateIn on your host (assuming virtual host www.node1.com), you can go to http://www.node1.com:8080/portal and click Sign in link. Then GateIn will send SAML Request to Salesforce and you will be redirected to Salesforce login screen. After login into Salesforce, you will be redirected to your GateIn and logged as the user which you logged in Salesforce . Again, username from GateIn is mapped to Federation ID in Salesforce, so GateIn user john is mapped to Salesforce user with Federation ID john )
Comments